Worried About Course Security? Start With Your Website.
LearnDash
MAY 6, 2021
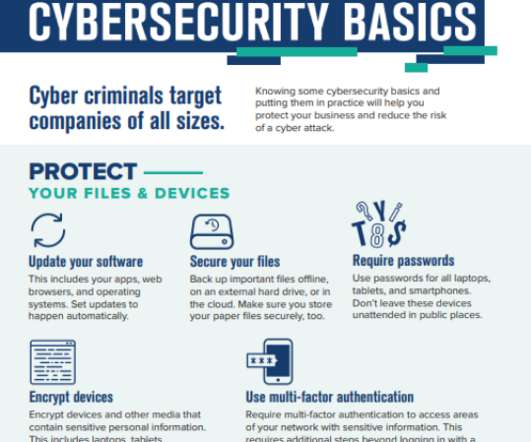
Protecting your intellectual property is important, but securing your website should come first. However, many of those concerned about a content stealing are actually behind the ball when it comes to the security of their own websites, and this poses a much more significant risk both to their learners, and to their business.


















































Let's personalize your content