OpenSesame announces partnership with Real Projects to expand business skills and information security course library
OpenSesame
JULY 20, 2020
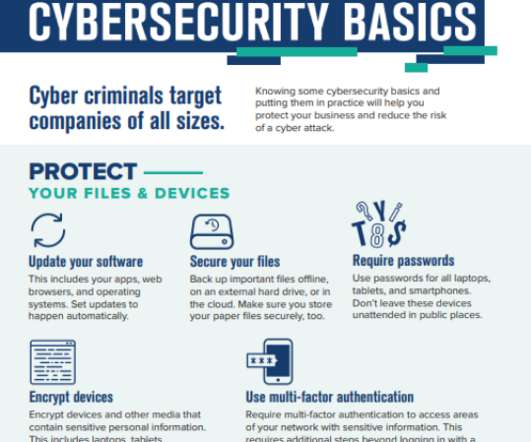
Global 2000 can now leverage critical training to improve business skills and information security in their organizations. Understanding that organizations have complex training needs, Real Projects offers a diverse course library created to address critical issues learners face in today’s work environment. .















































Let's personalize your content